Managed IT Services Cleveland 2026: The Future of IT Support and Business Strategy
Managed IT Services Cleveland 2026 – Contact the Pros Now
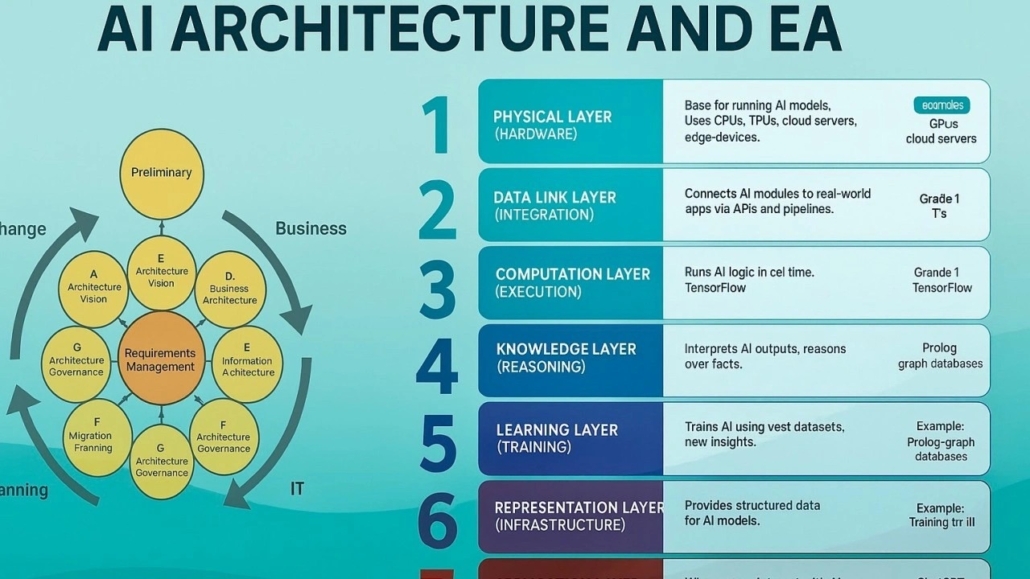
Predictive AI Monitoring & Automation for Managed IT Services Cleveland 2026
Image Source: Shadhin Lab LLC
Predictive AI monitoring is revolutionizing managed IT services by replacing reactive problem-solving with anticipatory intelligence. Cleveland businesses won’t wait for systems to fail by 2026. AI-powered platforms will spot potential disruptions before they affect operations. This radical alteration shows how forward-thinking organizations are approaching their IT infrastructure and support strategies differently.
Predictive AI Monitoring & Automation key features for Managed IT Services Cleveland 2026
Advanced managed services combine artificial intelligence with automation capabilities to change traditional monitoring methods. Modern AI-powered monitoring systems employ machine learning algorithms to set baseline performance metrics for networks, applications, and infrastructure. These systems analyze real-time data streams to detect anomalies before they become critical problems.
Key capabilities changing Cleveland’s managed services include:
- Real-time data analysis: AI systems process massive operational data volumes and spot patterns human analysts might miss while providing instant insights
- Automated remediation workflows: Pre-programmed response sequences trigger automatically when specific conditions appear, which reduces resolution time
- Intelligent alerting: Context-aware notifications cut alert fatigue by filtering noise and highlighting real threats
- Continuous learning: Systems become more accurate as they analyze outcomes and incorporate feedback
Agentic AI brings another game-changing advancement to this space. Unlike traditional monitoring tools, agentic AI works as autonomous “virtual coworkers” that can plan and execute complex tasks independently. These AI agents can analyze IT environments, make decisions based on knowledge, and take action without constant human oversight.
Predictive AI Monitoring & Automation business impact
AI-powered predictive monitoring creates measurable financial and operational advantages beyond technical improvements. Organizations that use these technologies report substantial improvements in key performance indicators that boost their bottom line.
Industry research shows AI-driven monitoring and automation systems cut stockouts by 72% and reduce excess inventory by 31%. Forecast accuracy at the SKU/location/day level jumps from 67% to 91%, while markdown losses drop by about $2.3 million yearly.
Cleveland businesses see these concrete benefits:
Dramatic downtime reduction: AI-powered prediction spots potential failures early, which enables preventive maintenance and reduces unplanned outages. Organizations typically see a 67% drop in system downtime within 90 days.
Operational efficiency gains: Businesses report higher productivity by automating routine maintenance and focusing staff on strategic work. AI-driven systems monitor critical application health, scale resources during peak times, and streamline workflows.
Better decision-making: Modern AI platforms turn reactive IT management into a proactive strategic function. Advanced simulations help businesses model various market scenarios and competitor moves to make smarter strategic choices.
Predictive AI Monitoring & Automation local relevance in Cleveland
Cleveland stands out as a regional hub for AI implementation, especially in monitoring and automation. The city combines research capabilities with growing AI-focused businesses and talent pipelines to create an environment where predictive technologies thrive.
The Cleveland Clinic–IBM Discovery Accelerator partnership forms the life-blood of this ecosystem. It brings hybrid cloud, high-performance computing, AI, and on-premises quantum hardware to the area. This work has created over 50 research projects while building educational paths between universities, government agencies, industry partners, and startups.
Local businesses benefit from this expertise through:
- Specialized AI talent pools trained in advanced monitoring techniques
- Regional knowledge-sharing networks focused on automation
- Research facilities developing advanced prediction models nearby
Cleveland retailers and service providers already see measurable benefits from AI monitoring solutions. AI-driven demand forecasting helps local businesses cut stockouts, reduce excess inventory, and save millions in markdown costs. This practical use proves the value—AI changes inventory management from reactive responses to anticipatory ordering.
Predictive AI Monitoring & Automation CTMS IT Advantage
Clinical Trial Management Systems (CTMS) show how predictive monitoring can boost operational efficiency across industries. Modern, cloud-based CTMS applications combine clinical information and processes for better efficiency and smooth trial information exchange. Organizations can manage complete end-to-end processes while seeing all activities from planning to execution.
CTMS monitoring offers several advantages that apply to managed IT services:
Real-time visibility and intelligence: CTMS platforms provide role-based dashboards with instant insights. Users can act at decision points without switching between multiple systems. Advanced IT monitoring platforms similarly offer consolidated views across infrastructure, applications, and security.
Proactive issue identification: CTMS helps teams spot and alleviate potential bottlenecks. Predictive IT monitoring similarly catches system problems, security risks, and performance issues early.
Continuous optimization: Modern monitoring platforms use AI to learn from past data. This improves prediction accuracy and reveals hidden optimization opportunities.
This proactive approach addresses potential issues before they affect operations. It marks a fundamental change from traditional break-fix models to strategic, anticipatory IT management.
Ready to learn about the power of [predictive AI monitoring?] Schedule Your Free 20-Minute IT Review to find how CTMS IT can revolutionize your infrastructure management from reactive to proactive for Managed IT Services Cleveland 2026.
Cleveland businesses can reduce operational disruptions and improve resource use with predictive AI monitoring and automation. Organizations that partner with forward-thinking managed service providers will gain competitive advantages through better reliability, efficiency, and strategic agility as AI capabilities advance through 2026.
Zero Trust Security & Compliance Integration

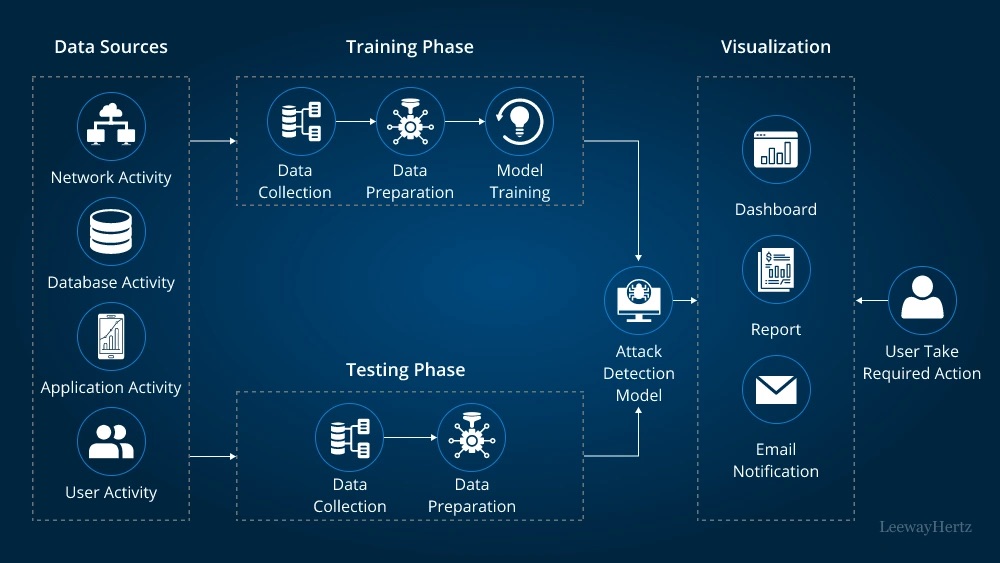
Image Source: LeewayHertz
Cleveland businesses are moving faster to adopt the Zero Trust security model as traditional network boundaries fade away in today’s hybrid work environments. This marks a basic change that sees all users, devices, and network traffic as possible threats. The old security methods assumed everything inside the network was safe. Zero Trust works on a simple yet powerful idea: “never trust, always verify”. This framework has become vital for companies facing sophisticated cyber threats and complex compliance needs.
Zero Trust Security & Compliance Integration key features
The Zero Trust security model changes how companies handle access control and data protection. It focuses on checking multiple factors before giving access to resources instead of just looking at network location.
A good Zero Trust system needs these key parts:
- Strict identity verification: Every user and device must pass authentication checks, whatever their location
- Least privilege access: Users get only the minimum permissions they need to do their jobs
- Microsegmentation: Networks split into secure zones to stop threats from spreading if breaches happen
- Continuous monitoring: Activity tracking happens in real-time to catch threats early
- Data-centric protection: Sensitive information stays safe through encryption and privacy tech wherever it lives
Modern Zero Trust systems also use machine learning to learn how users and devices normally behave. These systems check not just login details but also things like when someone logs in, where from, how secure their device is, and their usual work patterns.
The system’s policy engines use real-time risk checks to control access rules. Users face multiple checkpoints throughout their session, so security stays strong even after they log in.
Zero Trust Security & Compliance Integration business impact
Zero Trust brings big benefits beyond better security. It builds brand trust despite its name. Companies earn customer, employee, and partner trust because they stop one of the biggest trust killers: security breaches.
The business benefits show up in several ways:
Reduced breach impact: Microsegmentation and limited access rights stop attackers from moving around, which cuts down damage. Companies using Zero Trust say breaches do less harm because they stay contained.
Better user experience: Zero Trust can make work easier even with extra security layers. Users deal with fewer passwords thanks to single sign-on, while security stays strong through ongoing checks.
Cost savings: Companies save about USD 1.76 million per data breach with Zero Trust. Their long-term security costs drop by 31% through cheaper licenses and better hosting setups.
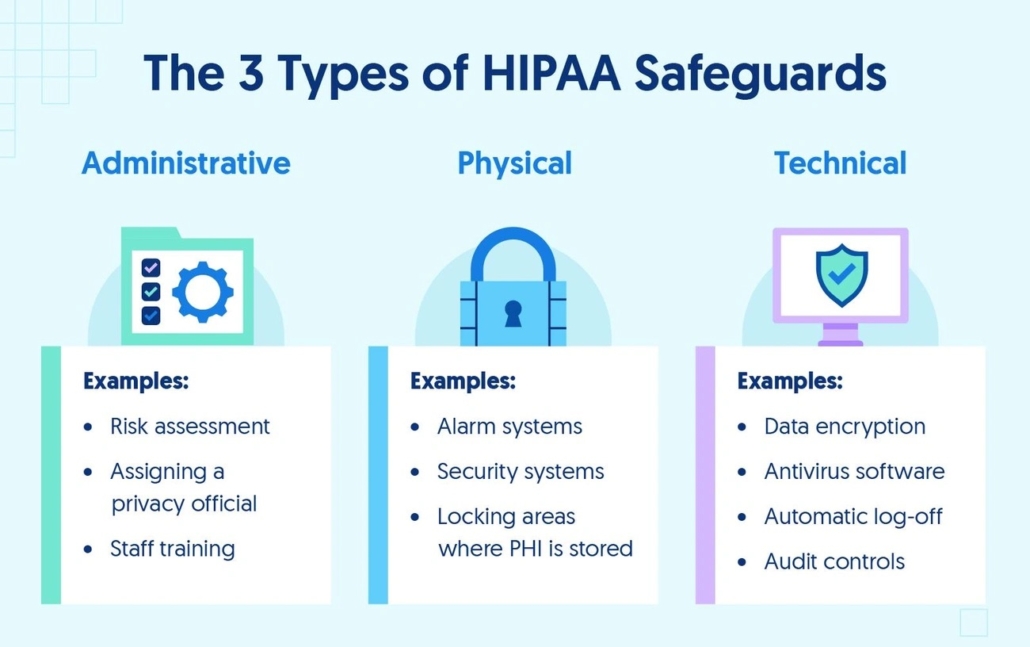
Better compliance: Zero Trust helps meet industry rules through real-time tracking and detailed audit trails. It lines up with rules like NIST 800-207 and cuts compliance risks from excess software rights.
Zero Trust helps companies grow. Customers who trust a business are 38% more likely to share their personal data. Over half will try new products. This trust lets companies test new offerings and create fresh experiences.
Zero Trust Security & Compliance Integration local relevance in Cleveland
Cleveland’s business environment makes Zero Trust especially important. Federal agencies with Cleveland offices must adopt Zero Trust practices by FY 2024 under OMB Memo M-22-09.
The city’s key industries—healthcare, manufacturing, and financial services—face strict regulations. Healthcare organizations in Cleveland’s medical community use Zero Trust to protect medical devices and patient data while offering secure telehealth services.
Is your Cleveland business ready to handle new security threats and compliance rules? Schedule Your Free 20-Minute IT Review with CTMS IT to check your readiness and see how Zero Trust can boost your security.
About 81% of organizations plan to start using zero trust strategies within a year. Cleveland businesses can work with expert service providers to get this knowledge without building their own security teams.
Zero Trust Security & Compliance Integration CTMS IT Advantage
CTMS IT helps Cleveland businesses set up Zero Trust systems through a step-by-step approach. Instead of changing everything at once—which often causes problems—we find specific areas where Zero Trust can help right away.
We start by creating a Zero Trust steering committee with business leaders. This makes sure security helps rather than blocks business goals.
The CTMS IT method includes: for (Managed IT Services Cleveland 2026)
- Teaching teams across departments about Zero Trust basics
- Mapping how people really work instead of just looking at job titles
- Setting clear rules for when automation stops and people take over
- Careful management of access rights as people join and leave
Cleveland businesses see real results from this approach. Companies stay compliant while moving fast to grab market opportunities. Our clients usually cut compliance costs by 60% through automation compared to manual checks.
CTMS IT helps Cleveland businesses tackle common Zero Trust challenges like old tools, insider threats, and employee pushback. We focus on building a Zero Trust culture through understanding rather than force. Our team explains why security matters and finds champions in each department to help spread the message.
Co-Managed IT Services for Hybrid Teams
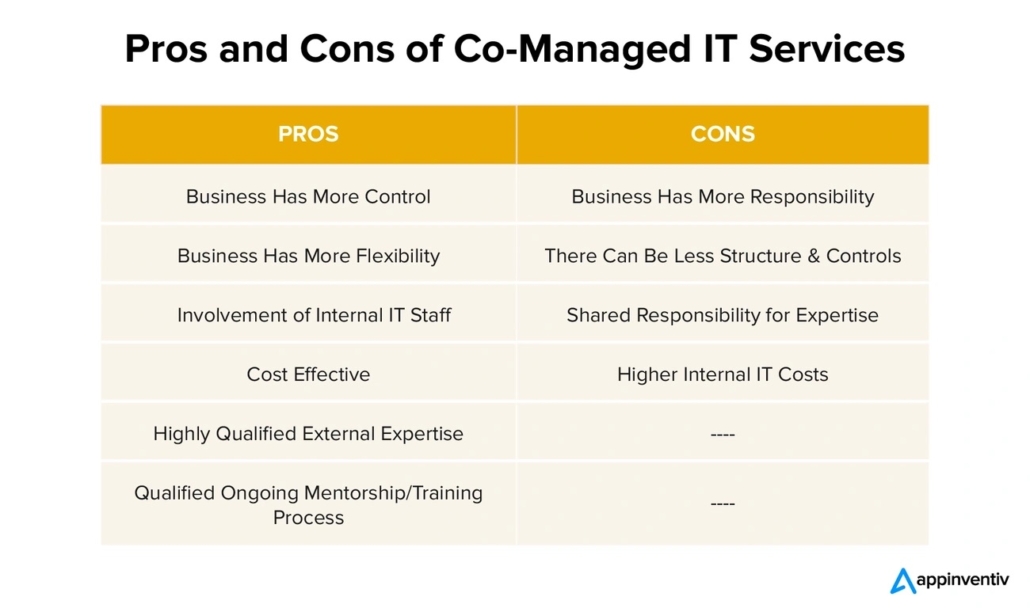
Image Source: Appinventiv
The way organizations manage their IT has changed dramatically with the rise of hybrid workplaces. Cleveland businesses will increasingly adopt co-managed IT services by 2026. This model creates a partnership where internal IT teams work with specialized managed service providers (MSPs). Companies can keep their internal expertise while getting access to specialized skills. The result is a powerful combination that handles modern business complexities effectively.
Co-Managed IT Services for Hybrid Teams key features
Co-managed IT has evolved beyond traditional outsourcing models. The service creates a customizable partnership between your internal staff and external specialists, unlike fully managed services where MSPs handle everything. Here are its distinctive capabilities:
- Flexible resource allocation: Organizations can choose what their technicians oversee and what the MSP handles, which naturally extends the existing IT team
- Complementary skill integration: Internal teams keep their company knowledge while MSPs bring specialized expertise in cloud migration, cybersecurity, and strategic planning
- Seamless division of responsibilities: In-house teams can manage daily operations while MSPs handle complex tasks requiring specialized expertise
- Strategic leadership options: Organizations can keep IT leadership internal while MSPs execute strategies, or they can use virtual CIO services for high-level guidance
Co-managed services become “a seamless extension of your business” rather than replacing internal expertise. This partnership model proves valuable as technology environments become more complex.
Co-Managed IT Services for Hybrid Teams Business Impact
Co-managed IT brings value beyond technical improvements with measurable financial and operational benefits. Companies using this model see substantial advantages:
Operational efficiency gains: Internal staff can focus on core business goals when MSPs handle repetitive or complex IT tasks. Both teams become more productive through this division of work.
Cost optimization: Companies save money through co-managed services in several ways. They avoid hiring full-time specialists while getting access to enterprise-grade tools that would cost too much to license alone. This approach helps maintain flexibility and reduce IT spending.
Enhanced resilience: Having two teams share responsibilities makes businesses stronger. Staff turnover, absences, or technical issues have less impact. Knowledge spreads throughout the organization instead of staying with just a few people.
Strategic flexibility: Co-managed arrangements let businesses adjust their resource allocation as needs change. Companies can scale their support during growth periods, special projects, or system changes without lengthy hiring processes.
Co-managed IT helps businesses turn their technology from a cost center into a growth engine that powers strategic initiatives.
Co-Managed IT Services for Hybrid Teams local relevance in Cleveland
Cleveland’s mix of healthcare, manufacturing, and financial services creates unique technology challenges. Co-managed IT fits these needs perfectly. Local organizations need to maximize efficiency while meeting compliance requirements and handling cybersecurity threats.
The shift to hybrid work environments in Cleveland has made flexible IT support essential. Local businesses must protect data across distributed networks while keeping productivity high. Co-managed services provide an ideal framework without requiring huge investments in new internal resources.
Is your Cleveland business struggling to balance IT needs with internal resources? Schedule Your Free 20-Minute IT Review to find how CTMS can improve your technology infrastructure through a customized co-managed approach.
Mid-sized businesses in Cleveland benefit most from co-managed arrangements. These organizations often have some IT capabilities but need more expertise in areas like advanced cybersecurity, cloud optimization, or regulatory compliance. They can get enterprise-grade expertise at reasonable costs through partnerships with managed service providers.
Co-Managed IT Services for Hybrid Teams CTMS IT advantage
CTMS gives Cleveland businesses a unique edge in co-managed IT services through its detailed, customized approach. We start by understanding your technology ecosystem and business goals before creating a tailored partnership.
The CTMS advantage includes:
Tailored technology solutions: We put our expertise to work strengthening your business technology strategies with solutions that fit your specific needs, not one-size-fits-all packages.
Seamless team integration: We blend with your staff and handle IT tasks that would distract your team from core business goals. This partnership ensures knowledge sharing and continuous improvement.
Cost-effective infrastructure management: You won’t see hidden fees or unexpected equipment costs with our technicians. CTMS helps you spend less on technology and staff while accessing enterprise-grade solutions.
Local expertise with global capabilities: We combine our deep knowledge of Cleveland’s business landscape with state-of-the-art technologies to keep your organization competitive in the digital marketplace.
CTMS provides the right mix of local support and advanced expertise for Cleveland organizations managing hybrid work environments. Our co-managed approach helps your business adapt to changing technology needs and builds a foundation for sustainable growth and innovation.
Cloud Optimization & Multi-Cloud Governance

Image Source: Warwick Communications
Cloud environments will evolve from simple storage solutions into complex ecosystems with multiple providers by 2026. This evolution creates opportunities and challenges for Cleveland businesses. Companies waste resources when they don’t optimize these intricate environments properly. Global cloud spending will exceed $1 trillion by 2028. Organizations must optimize their cloud systems to maximize technology investments while keeping performance and security intact.
Cloud Optimization & Multi-Cloud Governance key features
Cloud optimization today goes beyond simple cost-cutting measures and covers resource management in multiple cloud environments. These capabilities are changing Cleveland’s managed services landscape:
- Resource rightsizing: The system continuously lines up compute instances and storage with actual workload needs to eliminate overprovisioning
- Automated monitoring and analytics: AI-driven tools that spot usage patterns and suggest optimization opportunities
- Multi-cloud orchestration: Unified management platforms that give you visibility and control across AWS, Azure, Google Cloud, and private infrastructure
- Lifecycle management: Automated policies for data retention, snapshots, and instance scheduling based on business needs
Large enterprises have rapidly adopted multi-cloud strategies, with 92% now operating in multi-cloud environments. This change calls for sophisticated governance frameworks that standardize deployment models, implement automation, and employ cloud-agnostic tools to maintain consistency across platforms.
Cloud Optimization & Multi-Cloud Governance business impact
Companies that implement resilient cloud optimization strategies see tangible business results beyond cost savings. Well-managed cloud environments provide:
Better financial visibility: Consolidated dashboards offer immediate insights into spending patterns. Teams can avoid budget surprises and distribute costs appropriately across departments.
Operational efficiency: Right-sized resources and automated scaling ensure optimal application performance without extra costs. Some organizations cut cloud costs by 20-40% through strategic optimization.
Better compliance posture: Unified governance tools enforce consistent security and compliance policies in all cloud environments. This reduces risks from shadow IT and fragmented controls.
Is your organization maximizing the value of its cloud investments? Schedule Your Free 20-Minute IT Review to find how CTMS can optimize your multi-cloud environment for performance and cost efficiency.
Cloud Optimization & Multi-Cloud Governance local relevance in Cleveland
Cleveland businesses must balance innovation with cost control in cloud management. Local enterprises typically spend 23% of their IT budget on cloud management. This figure grows yearly as more workloads move to cloud environments.
The city’s industrial diversity creates complex cloud requirements that need specialized optimization strategies. Manufacturing firms need edge computing to process data closer to production facilities. Healthcare organizations require solutions that maintain compliance while enabling advanced analytics.
Cloud Optimization & Multi-Cloud Governance CTMS IT advantage
CTMS IT stands out through its structured approach to cloud optimization and multi-cloud governance. We implement a complete methodology that addresses Cleveland’s specific business challenges, unlike providers offering generic cloud management:
- Deep discovery process: We examine your current cloud footprint across all providers. Our team finds optimization opportunities based on actual usage patterns, not theoretical models.
- Custom FinOps framework: Our tailored financial operations approach lines up cloud spending with business outcomes. This makes costs predictable and eliminates waste.
- Unified visibility: Our consolidated dashboards provide immediate insights into performance, security, and costs across all cloud environments.
- Automated governance: Our policy engines enforce consistent security and compliance controls in all cloud environments. This reduces risk while enabling innovation.
24/7 Local Support & SLA-Driven Outcomes

Image Source: Systems X
Modern businesses can’t afford system outages at any time. Companies now consider local, round-the-clock IT support essential rather than optional. Service evaluation now relies on SLA-driven outcomes instead of traditional metrics. Cleveland businesses will make proximity their top priority when choosing managed IT providers by 2026—even with cheaper options available elsewhere.
24/7 Local Support & SLA-Driven Outcomes key features
Modern IT support goes beyond simple break-fix models. The technology infrastructure maintenance now comes with several key capabilities:
- Direct-to-technician access: Top providers connect their clients with skilled technicians in under 30 seconds. This eliminates frustrating hold times and complex escalation processes
- Multi-channel support options: Services come with phone, email, chat, and on-site help. Businesses can choose their preferred way to get assistance
- Outcome-based SLAs: Progressive providers now guarantee business outcomes that match customer goals instead of measuring traditional IT metrics
- Experience-level agreements (XLAs): These new frameworks prioritize employee satisfaction over technical metrics. About 87% of IT leaders say XLAs help them understand where support needs improvement
The industry has moved from reactive measurement to proactive business enablement. Modern SLAs focus on customer’s desired outcomes rather than arbitrary technical metrics. This prevents what experts call the “watermelon effect”—where metrics look green outside but customer experience stays red inside.
24/7 Local Support & SLA-Driven Outcomes business impact
24/7 local support creates value beyond technical assistance. It brings measurable improvements to operational effectiveness:
Better productivity: Reassigning IT tickets reduces end-user happiness by eight points. Employees lose two extra hours of work time on average. Local providers who fix issues quickly and correctly the first time help improve bottom-line results.
Budget efficiency: Local IT support often saves money, contrary to popular belief. About 91% of organizations that outsource help desk functions report costs are either lower (63%) or unchanged (28%) compared to in-house operations.
Business continuity: Local providers respond quickly to emergencies. Optimized support workflows reduce average incident resolution times from hours to just 18.5 minutes. Quick response helps minimize downtime during critical system failures.
24/7 Local Support & SLA-Driven Outcomes local relevance in Cleveland
Cleveland’s diverse economic landscape makes local IT support valuable. Healthcare, manufacturing, and professional services sectors need providers who understand specific compliance requirements and operational needs.
Is your Cleveland business receiving the responsive support it deserves? Schedule Your Free 20-Minute IT Review to find how CTMS IT can transform your support experience with locally-based, outcome-driven services.
24/7 Local Support & SLA-Driven Outcomes CTMS IT advantage
CTMS IT gives Cleveland businesses an edge through its detailed, outcome-driven approach to local support. Our SLAs focus on business outcomes that matter most to clients rather than just response times.
Our service level management follows both ITIL 4 principles and practical business needs. Each IT service gets its own SLA instead of using general agreements. This ensures precise service delivery rather than one-size-fits-all solutions.
CTMS takes a proactive approach unlike providers who just react to issues. Support becomes part of your strategic planning process. Our local presence enables quick remote and on-site support within minutes instead of days. Your business stays running even during difficult situations.
Comparison Table
| Service Area | Key Features | Business Effect | Cleveland Relevance | Implementation Benefits |
|---|---|---|---|---|
| Predictive AI Monitoring & Automation | – Immediate data analysis\n- Efficient remediation workflows\n- Smart alerting\n- Continuous learning | – 72% reduction in stockouts\n- 67% reduction in system downtime\n- 31% decrease in excess inventory\n- Forecast accuracy jumped from 67% to 91% | – Access to AI talent pools\n- Local knowledge-sharing networks\n- Close to research facilities | – Clear visibility and intelligence\n- Early problem detection\n- Ongoing optimization |
| Zero Trust Security & Compliance | – Strict identity checks\n- Minimal access rights\n- Microsegmentation\n- Ongoing monitoring\n- Data-focused protection | – $1.76M saved per data breach\n- 31% lower long-term security costs\n- Better brand trust | – Federal agency compliance rules\n- Healthcare sector security needs\n- Manufacturing security requirements | – 60% lower compliance costs\n- Better regulatory fit\n- Better data protection |
| Co-Managed IT Services | – Flexible resource use\n- Matching skill sets\n- Clear task division\n- Leadership options | – Better operations\n- Lower IT costs\n- Stronger organization\n- Flexible strategy | – Help for hybrid work setups\n- Special compliance knowledge\n- Enterprise-grade solutions | – Smooth team mixing\n- Economical infrastructure\n- Local know-how with global reach |
| Cloud Optimization & Multi-Cloud | – Resource sizing\n- Smart monitoring\n- Multi-cloud control\n- Lifecycle management | – 20-40% lower cloud costs\n- Better cost tracking\n- Better compliance standing | – 23% of IT budget goes to cloud\n- Industry-specific needs\n- Complex compliance rules | – Single view dashboard\n- Self-running governance\n- Custom FinOps system |
| 24/7 Local Support | – Direct tech access\n- Multiple support channels\n- Results-based SLAs\n- Experience guarantees | – 8-point rise in satisfaction\n- 91% report costs stayed same or dropped\n- 18.5-minute fix time on average | – Industry compliance help\n- Quick on-site response\n- Local business insight | – Ahead-of-time support\n- Quick problem solving\n- Goals that match yours |
Conclusion
Cleveland businesses face a technological crossroads as they approach 2026. Their competitive advantage will substantially depend on strategic IT decisions. Five key trends shape this landscape: predictive AI monitoring, Zero Trust security frameworks, co-managed IT partnerships, cloud optimization strategies, and 24/7 local support. These elements revolutionize how organizations build their technology infrastructure.
Cleveland’s business ecosystem needs specialized solutions. These solutions must tackle local challenges while tapping into global capabilities. Each trend brings its own benefits. Together, they create powerful foundations for operational excellence and growth. The data tells a compelling story: system downtime dropped by 67%, data breach costs decreased by $1.76 million, and cloud expenses fell by 20-40%. These are real outcomes, not theoretical projections.
Smart organizations now see technology decisions as boardroom priorities, not just IT department concerns. They have moved from fixing problems to developing strategies. This new approach changes how businesses invest in technology. Success depends on finding a partner who knows both Cleveland’s business landscape and emerging technologies.
CTMS IT delivers an integrated approach that lines up technological solutions with business goals. We created frameworks for AI implementation, security integration, and multi-cloud governance that solve Cleveland businesses’ daily challenges. Our local presence guarantees quick response times when every minute counts. Our strategic guidance helps transform technology from an expense into a growth catalyst.
Organizations that see IT as a strategic advantage will lead the future. Businesses must review their technology against current trends to find ways to improve. Make your IT a strategic asset with CTMS IT. Optimized infrastructure, better security, and predictable costs will help your Cleveland business thrive beyond 2026.
Key Takeaways
Cleveland businesses are transforming their IT strategies through five critical trends that deliver measurable results and competitive advantages by 2026.
• Predictive AI monitoring reduces system downtime by 67% while improving forecast accuracy from 67% to 91%, enabling proactive infrastructure management over reactive firefighting.
• Zero Trust security saves $1.76 million per data breach on average and reduces long-term security costs by 31% through continuous verification and microsegmentation.
• Co-managed IT services optimize resource allocation by combining internal expertise with specialized external skills, reducing costs while maintaining strategic flexibility.
• Multi-cloud optimization cuts cloud expenses by 20-40% through automated resource rightsizing and unified governance across multiple cloud platforms.
• 24/7 local support with outcome-based SLAs resolves incidents in 18.5 minutes on average, directly improving productivity and business continuity.
The convergence of these technologies creates a powerful foundation where IT transforms from a cost center into a strategic growth driver. Cleveland businesses partnering with knowledgeable managed service providers gain access to enterprise-grade capabilities without enterprise-level costs, positioning them for sustained competitive advantage in an increasingly digital marketplace.
FAQs
Q1. What are the key IT trends shaping Cleveland businesses in 2026? The major IT trends for Cleveland businesses in 2026 include predictive AI monitoring, Zero Trust security frameworks, co-managed IT services, cloud optimization strategies, and 24/7 local support with SLA-driven outcomes. These trends are transforming how organizations approach their technology infrastructure and strategy.
Q2. How can predictive AI monitoring benefit Cleveland companies? Predictive AI monitoring can reduce system downtime by 67% and improve forecast accuracy from 67% to 91% for Cleveland businesses. It enables proactive infrastructure management, identifies potential issues before they impact operations, and helps optimize resource utilization.
Q3. What is the impact of implementing Zero Trust security? Implementing Zero Trust security can save organizations an average of $1.76 million per data breach and reduce long-term security costs by 31%. It provides enhanced protection through continuous verification, microsegmentation, and data-centric security measures.
Q4. How does cloud optimization affect business costs? Cloud optimization strategies can cut cloud expenses by 20-40% for businesses. This is achieved through automated resource rightsizing, multi-cloud orchestration, and unified governance across multiple cloud platforms, leading to improved financial visibility and operational efficiency.
Q5. What advantages does 24/7 local IT support offer? 24/7 local IT support with outcome-based SLAs can resolve incidents in an average of 18.5 minutes, significantly improving productivity and business continuity. It provides rapid on-site response when needed, multi-channel support options, and a deep understanding of local business needs and compliance requirements.
Q6. How will managed IT services Cleveland 2026 evolve to meet new business challenges? By 2026, managed IT services Cleveland providers will move beyond traditional support to become strategic technology partners. Businesses will expect predictive AI monitoring, Zero Trust security frameworks, and advanced cloud governance built into every service.
This evolution means Cleveland companies can rely on managed IT services not only to maintain uptime and cybersecurity, but also to align technology investments directly with growth objectives. CTMS IT leads this shift by helping organizations anticipate disruptions, reduce downtime, and make data-driven business decisions through intelligent automation and 24/7 support.
Q7. Why should businesses invest in managed IT services Cleveland 2026 instead of traditional IT support?Traditional IT support reacts after issues occur, while managed IT services Cleveland 2026 are designed to predict and prevent them. This proactive approach uses AI-driven analytics, automated remediation, and constant performance monitoring to maintain seamless operations.
Cleveland businesses choosing forward-focused managed IT services benefit from predictable monthly costs, improved security compliance, and access to enterprise-grade expertise without the high overhead. Partnering with a trusted local provider like CTMS IT ensures your technology evolves with your business—not against it.