Boost Your Business with Managed IT Services for Small Businesses
What Are Managed IT Services for Small Businesses?
Image Source: Techlocity
Technology drives almost every aspect of business operations in today’s digital world. Many small businesses don’t have the resources or expertise they need to manage complex IT environments effectively. Managed IT services have become a game-changer in this scenario.
Managed IT services for small businesses provide a comprehensive solution that helps minimize downtime and enhance productivity.
Definition and scope of managed IT services
Your company can outsource its technology needs to a specialized third-party provider, known as a Managed Service Provider (MSP). Traditional tech support fixes problems after they occur. MSPs take a different approach by monitoring your business network continuously. They minimize IT problems and troubleshoot issues before operations get disrupted—all at a predictable monthly flat fee.
Investing in managed IT services for small businesses allows you to focus on your core operations while experts handle your IT needs.
Managed IT services offer a complete range of solutions, from daily network management to specialized tech solutions. Mobile device management, software as a service (SaaS), platform as a service, help desk support, and cloud backup solutions are some common services. Most MSPs provide all-inclusive packages with unlimited IT resources while hired. This ensures your technology infrastructure stays stable and secure.
With managed IT services for small businesses, you can ensure that your technology is always up to date and secure.
How MSPs differ from traditional IT support
MSPs and traditional IT support differ mainly in their approach. Traditional IT support uses a “break-fix” model—something breaks, you call for help, and wait for repairs. Businesses lose valuable time while waiting for solutions with this reactive approach.
Choosing managed IT services for small businesses can significantly reduce the risk of data breaches and cyber threats.
Managed IT services for small businesses help ensure that you have access to the latest technology without the associated costs.
Many small businesses rely on managed IT services for small businesses to streamline their operations and improve efficiency.
Utilizing managed IT services for small businesses can lead to significant decreases in operational costs.
The benefits of managed IT services for small businesses include not just cost savings but also enhanced security measures.
Managed IT services for small businesses provide the necessary resources to compete effectively in today’s market.
Managed IT services work differently. They operate continuously in the background to predict potential disruptions and prevent them proactively. MSPs use a highly technical pool of experts specific to supported applications. This gives businesses access to current skill sets without the costs of training in-house staff.
By leveraging managed IT services for small businesses, companies can improve their response times to IT issues.
MSPs also work under contractual service level agreements (SLAs). These agreements clearly define response times and resolution expectations, which ensures accountability and consistent service quality.
Why small businesses are turning to MSPs
Managed IT services for small businesses can effectively reduce the burden on in-house IT staff, allowing them to focus on strategic initiatives.
With managed IT services for small businesses, you gain peace of mind knowing your systems are monitored 24/7.
Access to managed IT services for small businesses ensures that you are not alone in managing your technology challenges.
Adopting managed IT services for small businesses can help companies adapt to changing technology landscapes.
Small businesses are adopting managed IT services rapidly for several good reasons. They face the same cybersecurity threats, software needs, and compliance requirements as large enterprises. The challenge is they have fewer internal resources and tighter budgets.
One of the key advantages of managed IT services for small businesses is their ability to offer customized solutions tailored to specific needs.
Maintaining compliance is easier with managed IT services for small businesses, as providers stay updated on regulations.
Managed IT services for small businesses allow for faster configurations and deployment of IT solutions.
Investing in managed IT services for small businesses can help drive innovation and competitiveness in the market.
To stay ahead, consider how managed IT services for small businesses can transform your operations.
Industry research shows that 44% of businesses use service providers because they lack the bandwidth to handle certain IT tasks, even with in-house expertise. The numbers are compelling – 87.5% of SMBs either currently use an MSP or plan to partner with one.
Managed IT services for small businesses enable teams to focus on delivering value rather than troubleshooting issues.
Business continuity is enhanced through managed IT services for small businesses, ensuring minimal disruption.
Small businesses value the risk mitigation that comes with consistent network monitoring instead of reactive crisis management. MSPs give access to enterprise-level IT capabilities at a fraction of the cost. Business owners can focus on their core operations without worrying about technology functionality.
Collaboration improves when utilizing managed IT services for small businesses, as technology becomes more accessible.
Managed IT services for small businesses can assist in making informed decisions backed by data analytics.
These services also contribute to environmental sustainability by optimizing resource usage for managed IT services for small businesses.
Understanding your needs is vital when selecting managed IT services for small businesses to achieve the best results.
Key Benefits of Managed IT Services
Small business owners are finding many more advantages of managed IT services that go way beyond the reach and influence of simple tech support. These detailed solutions offer strategic benefits that can transform how companies operate in today’s technology-driven environment.
Cost savings and predictable monthly pricing
Small businesses turn to managed IT services to save money, and with good reason too. Studies show that businesses partnering with MSPs can reduce their IT costs by 25-45%. It also helps increase operational efficiency by 45-65%.
The flat-fee pricing model replaces unpredictable IT expenses with a consistent monthly investment. Business owners can budget better and avoid financial shocks from unexpected tech emergencies. Small businesses spend approximately USD 40,000 per year on IT support, while an in-house IT manager’s average annual salary reaches USD 113,000.
Access to expert support and latest technologies
MSPs give small businesses access to a diverse team of IT professionals, including product experts, system engineers, and virtual chief information officers. Building this expertise in-house would cost too much.
MSPs specializing in managed IT services for small businesses can enhance your overall business strategy.
Effective deployment of managed IT services for small businesses can lead to increased employee satisfaction and performance.
Investing in managed IT services for small businesses is a strategic move towards future-proofing your operations.
Companies report that outsourcing IT helps them access skillsets unavailable internally (46%). This benefit includes advanced technologies since MSPs maintain partnerships with leading technology vendors and offer enterprise-grade solutions at competitive prices.
Scalability and flexibility for growing businesses
Your IT needs change as your business grows. Managed IT services let you scale resources up or down based on current requirements. Small businesses find this flexibility valuable, especially when they face seasonal changes or rapid growth.
You can scale both infrastructure and service levels. MSPs can adjust their support as you add new users, deploy more services, or expand into new markets. Your technology backbone will grow alongside your business goals.
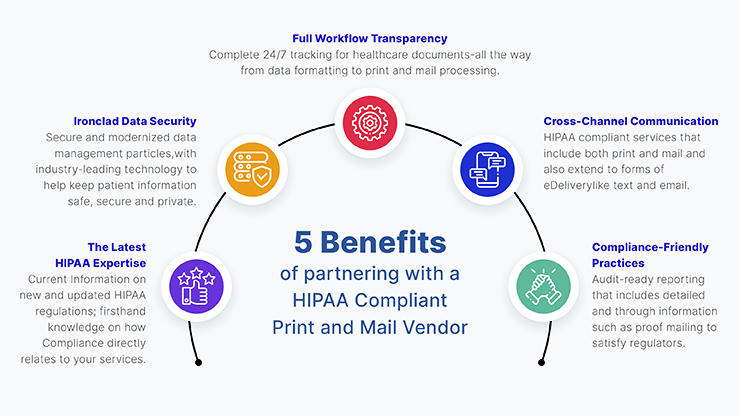
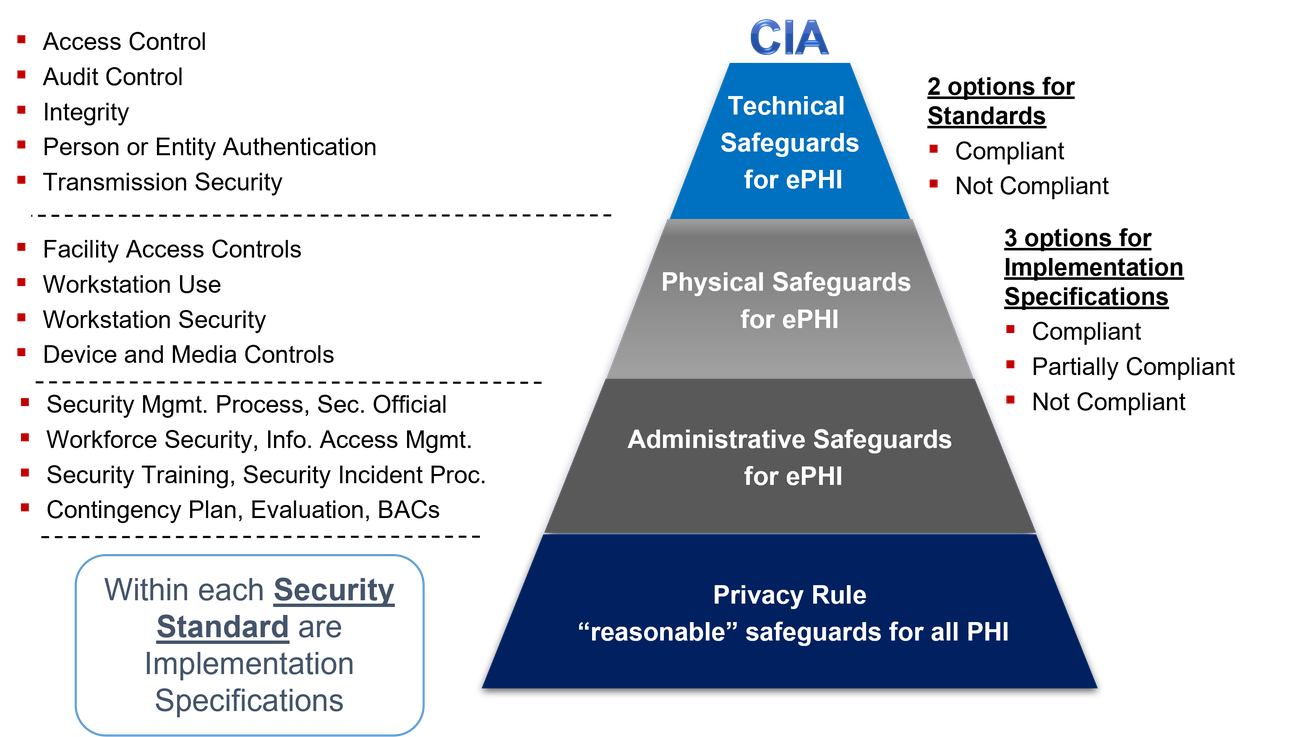
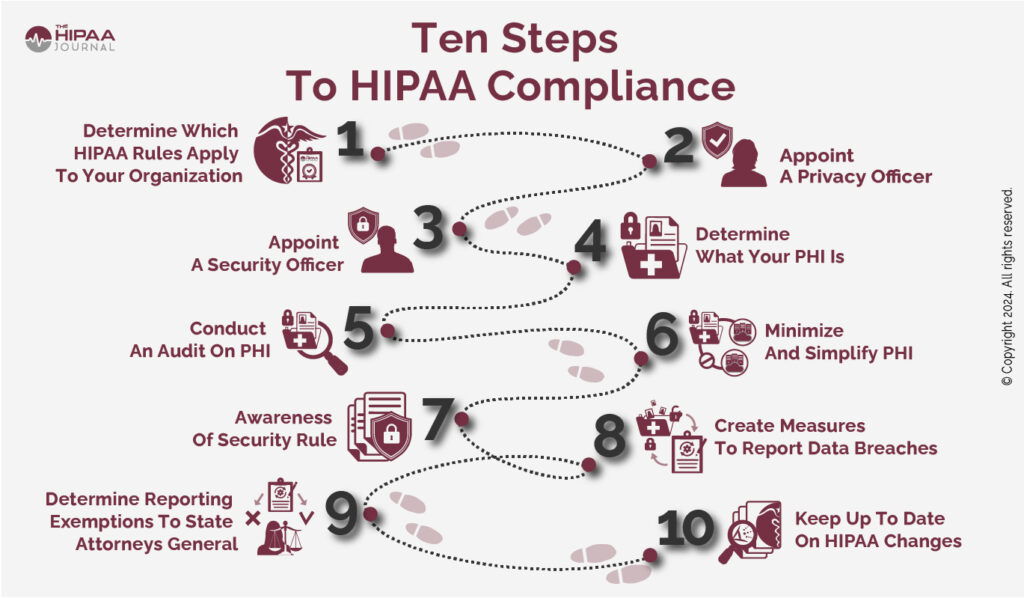
Improved cybersecurity and compliance
Strong security is essential with cyber threats increasing. Last year, 73% of SMBs faced a cyberattack or data breach—up from 43% the previous year. MSPs set up detailed security measures including firewalls, intrusion detection systems, and encryption technologies to protect your digital assets.
MSPs also help you handle complex regulations. They ensure your business meets industry-specific standards like HIPAA for healthcare, PCI-DSS for payment processing, or GDPR for handling EU citizens’ data.
Reduced downtime and faster issue resolution
With the right managed IT services for small businesses, your company can achieve technological advancements.
Downtime hits businesses hard financially. Small to medium-sized businesses can lose upwards of USD 300,000 per hour. Managed IT services reduce these disruptions through proactive monitoring and maintenance.
MSPs spot and fix potential issues before they affect your operations to maintain business continuity. Quick response times and 24/7 monitoring ensure immediate attention when technical issues arise.
Ready to turn your IT from a business challenge into a competitive advantage? Contact CTMS IT to learn how we can help you today!
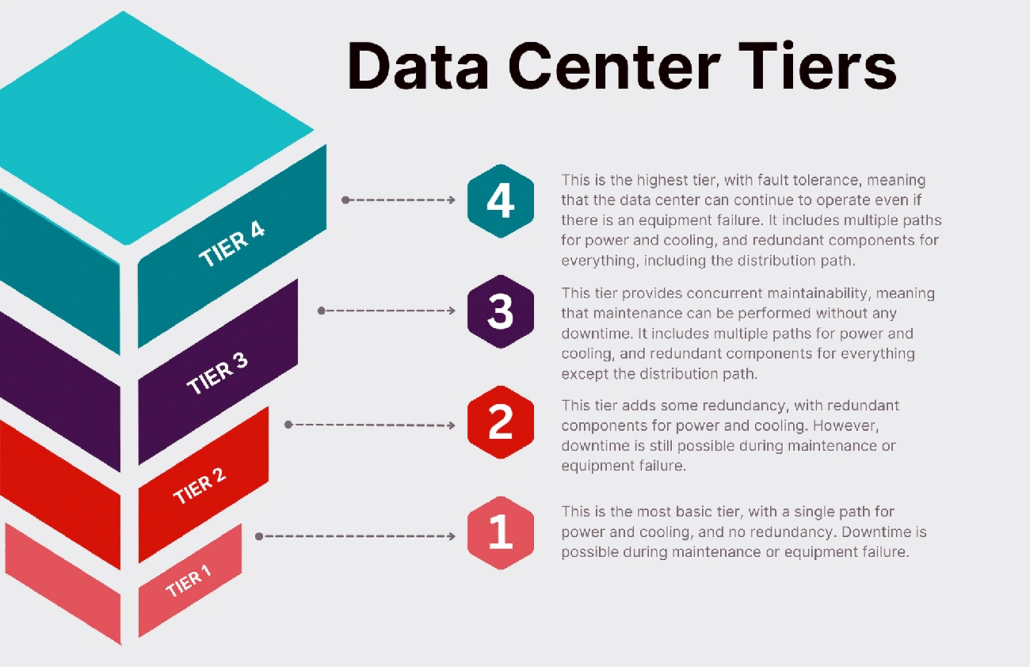
Core Services Offered by MSPs
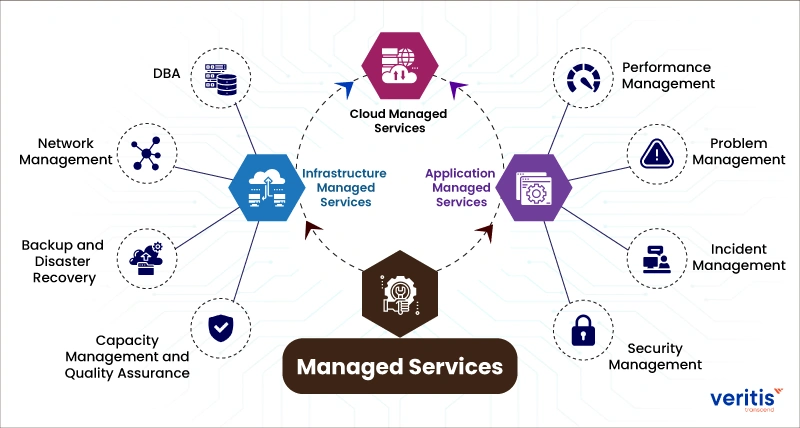
Image Source: Veritis
MSPs provide a complete set of IT solutions that help small businesses work efficiently in today’s tech-driven world. Here are the main services MSPs offer their clients.
1. Network and server monitoring
Today’s MSPs use advanced tools to monitor your network infrastructure’s health and performance continuously. They track critical metrics like uptime, bandwidth usage, and device performance through technologies such as SNMP (Simple Network Management Protocol). This allows them to spot potential problems before they affect your business operations.
Network monitoring services include:
- Live alerts when performance metrics deviate from normal ranges
- Traffic analysis to spot bottlenecks or suspicious activity
- Automatic detection of new network devices
- Regular performance reports and trend analysis
2. Cybersecurity and threat protection
Security has become essential as cyberattacks grow more sophisticated. Studies show 63% of small businesses face ransomware and advanced threats. MSPs apply multi-layered security strategies that include:
Advanced endpoint protection works better than traditional antivirus by using AI-powered solutions to detect and stop malware, ransomware, and zero-day attacks. Many MSPs now actively hunt for threats to find vulnerabilities before attackers can exploit them.
3. Data backup and disaster recovery
Your business’s survival depends on reliable backup systems and recovery plans. MSPs set up complete backup solutions to protect your critical data. Industry experts note that 40% of small businesses never reopen after a disaster.
MSPs develop disaster recovery plans that fit your business needs and test backups regularly to ensure successful restoration when needed. This strategy keeps downtime minimal and helps maintain operations during major disruptions.
4. Help desk and remote support
Technical support is the lifeblood of managed IT services. MSPs offer support through multiple channels – phone, email, web chat, mobile app, or web portal. Your employees can get help whenever problems occur, which keeps productivity losses minimal.
Technicians can fix many issues remotely without visiting your site. This approach cuts resolution times significantly and keeps your team working efficiently.
Choosing the right strategy for managed IT services for small businesses can set you apart from your competition.
5. Cloud services and migration
MSPs help businesses utilize cloud technologies to improve flexibility and cut capital costs. Their services cover cloud migration planning, setup, and ongoing management of cloud resources.
As more businesses adopt hybrid environments, MSPs provide expertise to integrate on-site systems with cloud services. This ensures smooth operations across all platforms.
6. IT asset and vendor management
MSPs track hardware and software throughout their lifecycle to manage IT assets effectively. They maintain detailed inventories and monitor warranties, usage patterns, and performance metrics to optimize your technology investments.
The vendor management service coordinates with multiple technology providers, handles contracts and renewals, and ensures you get proper support. Your internal staff faces less burden, and service levels stay consistent across your IT ecosystem.
How to Choose the Right Managed IT Provider
Managed IT services for small businesses create an infrastructure that supports growth and innovation.
The right managed IT service provider can make or break your business operations. Your choice will determine the quality of service that lines up with your business needs and goals.
Evaluate service offerings and SLAs
Service Level Agreements (SLAs) are the foundations of your relationship with an MSP. These agreements spell out your services and measurement criteria. We focused on response times, resolution expectations, and uptime guarantees. A well-laid-out SLA should include specific metrics that make the provider accountable for service quality.
You should ask potential MSPs for sample SLAs to understand their commitment levels. The provider should be clear about consequences when service levels fall short—good SLAs include remediation terms and service credits.
Check certifications and industry experience
The best MSPs invest in certifications to confirm their expertise. You should look for CompTIA A+ and Network+, Microsoft Azure certifications, CISSP (Certified Information Systems Security Professional), and ITIL. These credentials show their steadfast dedication to staying current with technology.
Experience in your industry matters as much as certifications. References from businesses your size and in your sector will help you understand how well they know your challenges.
Understand pricing models and hidden costs
MSPs offer various pricing structures—per-user, per-device, tiered, and all-inclusive models. Each option works better for different business needs. To cite an instance, per-user pricing makes sense if your employees use multiple devices. Tiered pricing gives you flexibility in service levels.
Watch out for setup fees, overage charges, and after-hours support costs. Industry data shows managed IT services cost between USD 100.00 to USD 250.00 per user monthly, based on service level.
Look for local support and responsiveness
Think over whether you need on-site support or can work with remote-only help. Local providers give you faster on-site response, better regional business insight, and face-to-face relationships.
Quick response is a vital factor—check each MSP’s guaranteed response windows and availability. Many top MSPs provide 24/7/365 support and respond within 15 minutes to critical issues.
Ask about onboarding and transition process
Moving to managed IT services needs a systematic approach. Quality MSPs use a detailed onboarding process that includes discovery, assessment, and operational integration.
Ask about their transition methods, documentation practices, and team training. Smooth transitions should include shadowing sessions, service documentation, and clear communication throughout.
Need help finding the right managed IT provider for your small business? Contact CTMS IT to learn how we can help you today!
Conclusion
The Strategic Advantage of Managed IT Services
Small businesses with complex technology needs now see managed IT services as a strategic advantage. This piece shows how MSPs provide complete IT solutions with predictable monthly rates. Traditional break-fix models, on the other hand, often result in expensive downtime and reactive troubleshooting.
The financial benefits speak for themselves. Small businesses can access enterprise-level expertise at 25-45% lower costs compared to in-house IT departments. Better budget planning and resource allocation become possible with predictable monthly billing.
MSPs offer services that were once limited to larger enterprises. These include network monitoring, cybersecurity, cloud management, and disaster recovery. Small businesses can now compete better thanks to this technology becoming accessible to more people.
Cybersecurity needs special attention. Statistics show that 73% of SMBs faced cyberattacks or data breaches. MSPs build resilient security frameworks that small businesses would struggle to create on their own.
Businesses should review potential MSPs carefully based on their service offerings, industry experience, pricing transparency, and response capabilities. The right provider becomes part of your team rather than just another vendor.
Managed IT services for small businesses let business owners concentrate on growth while avoiding technology problems. Contact CTMS IT to learn how we can help you today! Your business can turn technology into a real competitive advantage with the right MSP partnership.
FAQs
Q1. What are the main benefits of managed IT services for small businesses? Managed IT services for small businesses offer cost savings, access to expert support, improved cybersecurity, reduced downtime, and scalability. Small businesses can benefit from enterprise-level IT capabilities at a fraction of the cost, allowing them to focus on core operations while ensuring their technology infrastructure remains stable and secure.
Q2. How do managed IT services for small businesses differ from traditional IT support? Managed IT services for small businesses take a proactive approach, continuously monitoring networks and addressing issues before they cause disruptions. Traditional IT support follows a reactive “break-fix” model. Managed services providers (MSPs) offer comprehensive, ongoing support with predictable monthly pricing, while traditional support typically involves ad-hoc problem-solving.
Q3. What core services do managed IT providers typically offer? Core services usually include network and server monitoring, cybersecurity and threat protection, data backup and disaster recovery, help desk and remote support, cloud services and migration, and IT asset and vendor management. These services are designed to cover all aspects of a small business’s IT needs, including managed IT services for small businesses.
Q4. How much do managed IT services for small businesses typically cost? Managed IT services for small businesses generally cost between $100 to $250 per user per month, depending on the level of service. This pricing model often results in cost savings of 25-45% compared to maintaining an in-house IT department, making it an attractive option for small businesses.
Q5. What should I consider when choosing a managed IT service provider? When selecting an MSP for managed IT services for small businesses, evaluate their service offerings and SLAs, check certifications and industry experience, understand their pricing model and potential hidden costs, consider their local support and responsiveness, and inquire about their onboarding and transition process. It’s important to choose a provider that aligns with your business needs and can serve as a true extension of your team.