IT Managed Services Near Me: How Smart Businesses Stay Secure, Compliant, and Ahead in 2026
Businesses now turn to “IT managed services near me” searches when technology challenges become overwhelming. We’ve all experienced those frustrating moments – system crashes during critical presentations, network slowdowns that appear from nowhere, and cybersecurity threats that seem to lurk everywhere.
Reliable IT service providers are essential to business survival today. Companies often learn this lesson after their systems crash at the worst moments. Local managed IT services companies deliver something that sets them apart from national providers – they offer quick response times with customized attention. Local providers rush to your site faster when emergencies strike, even though larger corporations might showcase impressive client portfolios.
The digital world keeps changing rapidly. Research shows that companies can better predict their IT costs while getting excellent technical support by partnering with managed IT services. Small and mid-sized businesses now prefer local experts over in-house solutions because they strike the perfect balance between cost control and service quality.
Smart businesses partner with local IT providers to remain competitive, compliant and secure as we approach 2026.
Why ‘Near Me’ Matters More Than Ever

Image Source: WCA Technologies
The concept of “near me” has changed how IT services are delivered today. Local address isn’t the only factor anymore. Location plays a bigger role than ever for managed IT services in 2026. Let me tell you why.
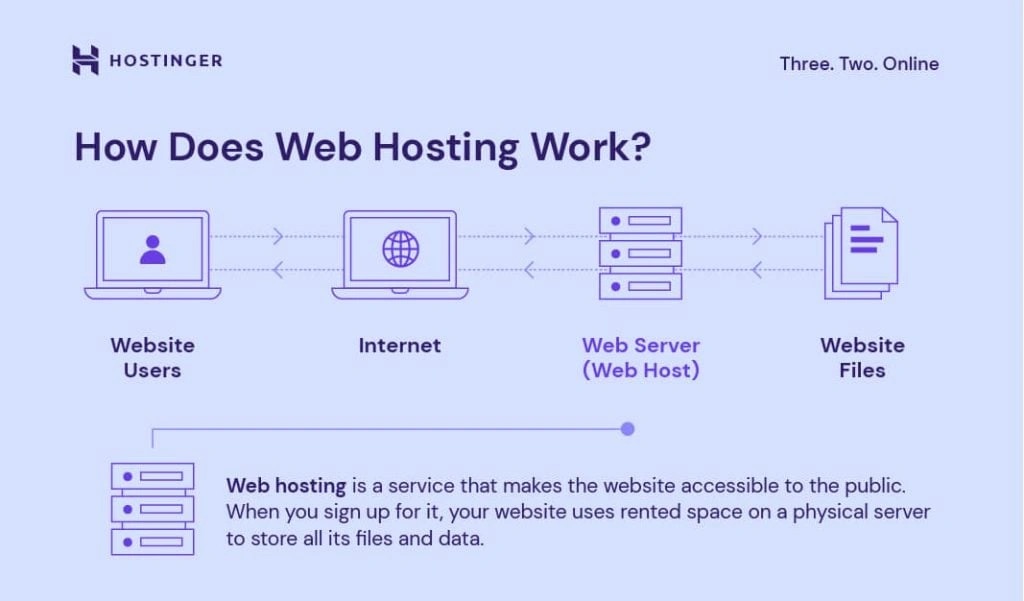
Redefining proximity in IT managed services
IT services now go way beyond geographic boundaries. Recent research shows that while location still matters, other aspects like cognitive, social, organizational, and institutional proximity are just as vital. These elements shape how resources interact and coordinate within business ecosystems. Your IT service provider’s ability to support your business depends on all these factors.
The digital world has changed how proximity works. It opens new doors for business activities while making physical location less important. Yet physical closeness still holds value—it just works together with other types of connections now.
Companies see better results when their teams work side by side. This has led them to rethink the old outsourcing models that only looked at cutting costs. Today’s businesses want providers who can offer:
- Easy access to key stakeholders
- A diverse pool of specialists
- Team environments that lead to state-of-the-art solutions
Proximity goes beyond just location—it includes culture, communication, and compliance. When operations line up well, projects stay on track with fewer mistakes. Time zones and work habits that match make everything run faster through quick decisions and smooth teamwork.
CTMS IT’s local presence in Ohio and Texas
Computer Technology Management Services (CTMS) has been a trusted IT resource in Ohio and the Midwest for over 10 years. They’ve become a revolutionary force in cybersecurity support, cloud computing, managed IT consulting, and business phone services.
CTMS creates solutions for clients of all types across several industries. Their method includes:
- Understanding your goals
- Creating practical technology plans
- Looking at budgets to avoid surprises
The core team works hard to keep your technology safe, secure, and flexible. This applies to school administrators, healthcare practitioners, and legal clerks alike. Their industry knowledge helps CTMS give better service than big national providers.
Why local response time beats national scale
A local managed service provider beats the competition with quick response times. Local providers can be at your door quickly, while remote MSPs might take hours or days. Quick troubleshooting stops small problems from becoming big headaches.
Here’s how response times compare:
- Most local MSPs: On-site emergency help within 2-4 hours, sometimes guaranteed same-day
- National providers: 24-72 hours for on-site support
This time difference becomes crucial during system failures. Hardware problems or network crashes need quick fixes. Waiting for far-away technicians means more downtime and lost money. Of course, remote fixes work for many issues, but sometimes you just need someone there in person.
Local providers give more individual-specific service because they know your business, industry, and market. Face-to-face talks help them understand your IT setup better and offer solutions that fit your needs. This personal touch makes a big difference, and having someone who gets your challenges builds trust.
Local managed service providers also know the specific laws, rules, and compliance requirements in your area. This knowledge keeps your IT systems following local standards and helps avoid fines and legal trouble.
From setup to support to planning for the unexpected, local IT providers give personal service that others can’t match. Being there in person makes users happier and builds stronger relationships between your staff and the provider. Quick chats during visits often reveal new business goals that technology can help achieve.
The need for local IT expertise will grow by 2026 as rules get more complex and security threats increase. The “near me” in your IT managed services search isn’t just about location—it’s about finding a partner who knows your business environment and can help right away when critical systems fail.
The Hidden Cost of Poorly Managed IT
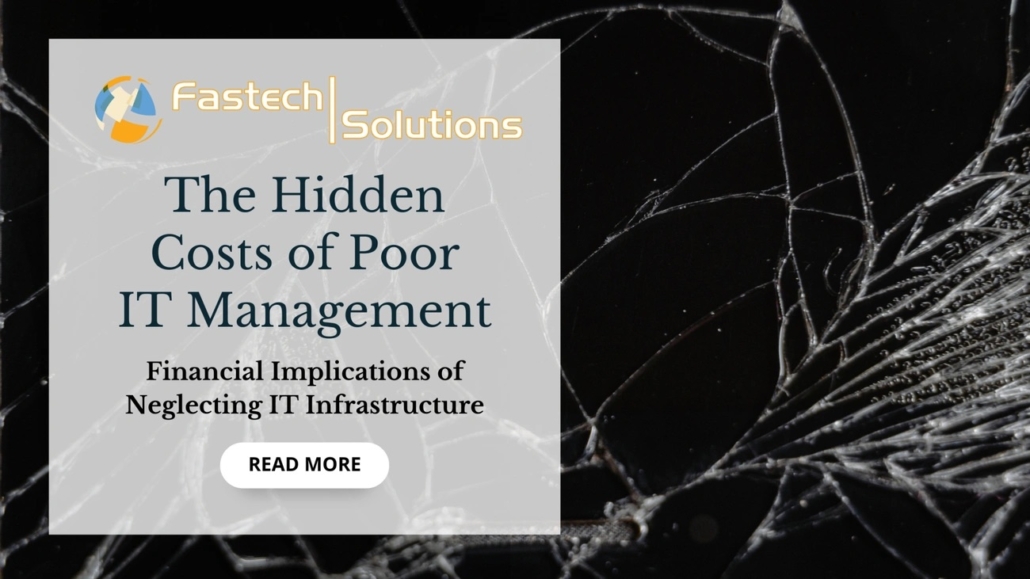
Image Source: Fastech Solutions
Poor IT management isn’t just annoying—it’s a financial nightmare waiting to explode. Companies often don’t realize how badly neglected tech infrastructure can hurt them until they face massive costs that eat away at profits and stop growth dead in its tracks.
Downtime and its financial impact
IT downtime hits companies hard and fast in their wallet. Studies show that unplanned downtime costs organizations $5,600 every minute—adding up to $336,000 per hour. The numbers get even scarier for Fortune 1000 companies, where costs can reach $1 million per hour.
The price tag changes based on company size and industry:
- Financial services lose about $152 million each year from downtime
- Small businesses take a $55,000 hit in yearly revenue from IT failures
- Mid-size companies face losses over $91,000 per year
- Large corporations can lose more than $1 million annually
Money lost from downtime is just the beginning. Financial institutions’ revenue losses ($37 million) make up only 25% of what downtime costs them. They also get hit with regulatory fines ($22 million) and legal fees ($14 million).
These problems get worse the longer they last. Companies take about 277 days to spot and fix a cybersecurity breach. The situation has gotten worse over time. Almost 30% of reported outages in 2021 lasted more than 24 hours—up from just 8% in 2017.
Security breaches and compliance fines
Security breaches hit companies with a double whammy: immediate cleanup costs and long-term penalties. Data breaches now cost companies $4.45 million on average in 2023—up 2.3% from 2022.
The bill includes:
- Emergency IT support and specialist help
- System recovery and data restoration
- Ransomware payments (averaging $600,000 in 2023)
- Lost business and revenue
- Legal fees and settlements
Breaking compliance rules makes everything much worse. Companies that don’t follow rules pay $2.3 million more for data breaches than those who do. Regulators don’t mess around with fines:
- HIPAA violations cost up to $1.5 million yearly
- GDPR non-compliance hits €20 million or 4% of global turnover
- PCI DSS violations range from $5,000 to $100,000 monthly
Smart tech choices can save serious money. IBM found that companies using AI for security saved $1.76 million compared to those without it.
Real-life examples of IT mismanagement
Big companies have learned these lessons the hard way. Their stories show exactly what poor IT management costs.
Marriott’s nightmare began in 2018 when poor risk management led to hackers stealing personal and financial data from 500 million guests. Equifax dropped the ball in 2017 when security vulnerabilities exposed 140 million people’s data.
Target’s 2013 mess exposed 40 million credit cards and 70 million customers’ personal info, landing them with an $18.5 million fine for breaking PCI DSS rules. Capital One’s 2019 breach exposed over 100 million customers’ sensitive data and cost them $80 million in fines.
Tech giants aren’t bulletproof either. Apple lost $25 million during a 12-hour store outage in 2015. A global IT crash in 2024 messed up payment systems worldwide, forcing businesses back to cash.
Small and medium businesses might not survive such hits. Gartner’s research shows that 94% of companies don’t make it after severe data loss. After losing computer records, 43% of businesses close immediately, and another 51% shut down within two years.
The root cause often lies in how people handle IT, not the technology itself. Companies struggle not because they lack good data, but because they manage it poorly. The Beirut explosion shows this perfectly—officials knew about dangerous materials but failed to act because of bad information management.
Get Your Free IT Assessment — See Why Businesses Across Ohio, the Midwest & Texas Rely on CTMS IT.
Professional IT management does more than fix tech problems—it protects your entire business. Strategic planning, constant monitoring, and deep compliance knowledge turn technology from a liability into a powerful tool that drives growth.
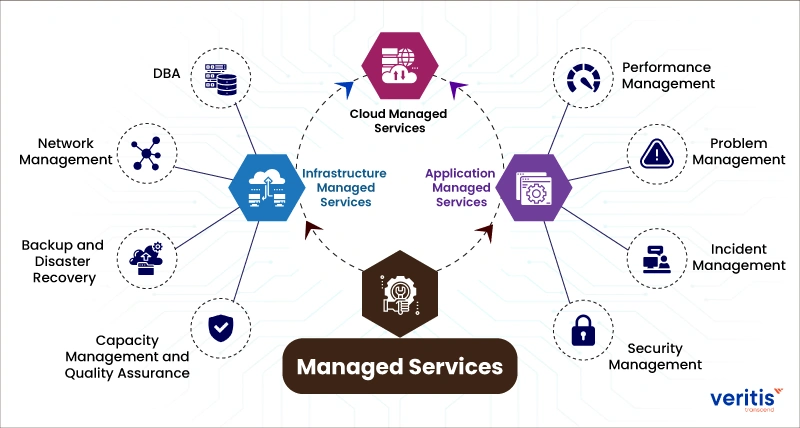
What World-Class IT Managed Services Actually Deliver
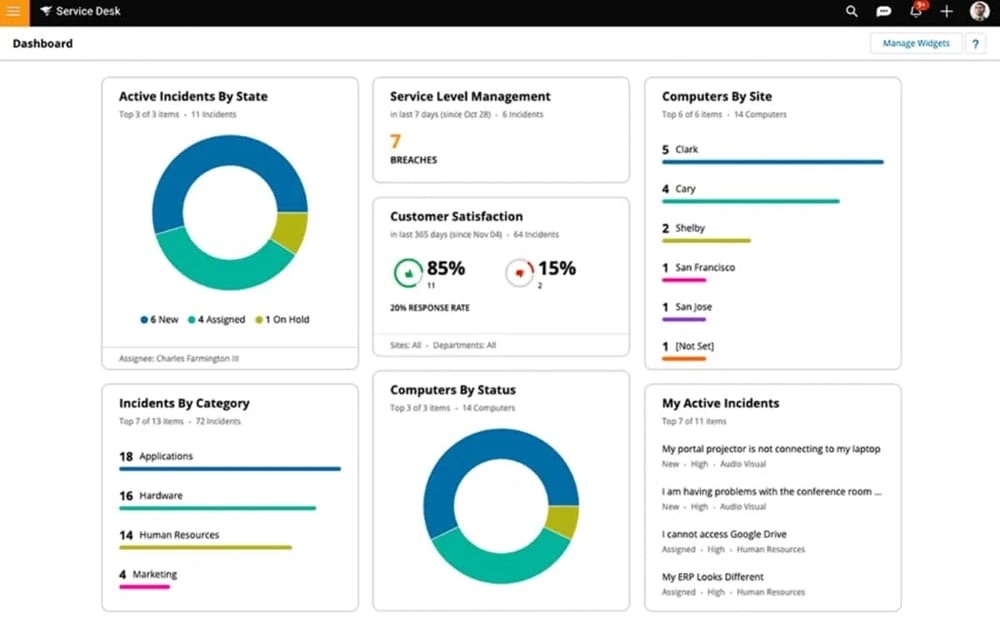
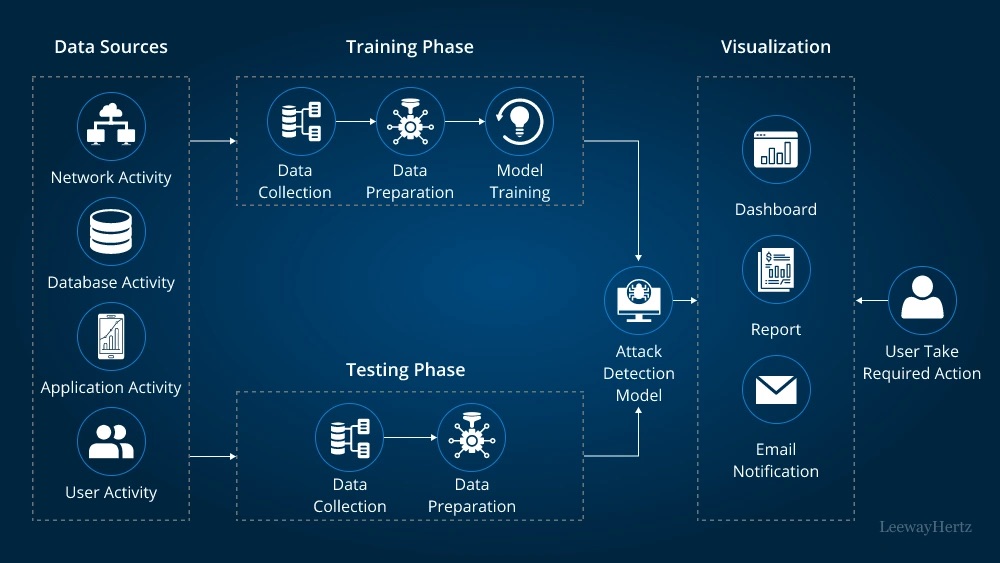
Image Source: Channel Insider
World-class IT managed services offer much more than simple technical support. Modern businesses just need service providers who can deliver complete solutions to address today’s challenges. Let’s get into what makes world-class IT managed services stand out from regular offerings.
Always-on monitoring and fast response times
Businesses facing new threats need round-the-clock cybersecurity monitoring. This watchfulness changes your security stance from reactive to proactive and identifies threats before they gain system access. The detection time difference tells a compelling story—without 24/7 monitoring, hackers can stay hidden for 280 days, which means almost ten months of unauthorized access.
Two key metrics show why timing is crucial: Mean Time to Detect (MTTD) and Mean Time to Respond (MTTR). Top providers reduce both timeframes and spot threats within minutes. To cite an instance, CTMS IT’s critical support ticket response averages 15.6 minutes—much faster than the industry’s 4-hour standard.
Quick incident response capabilities ensure threat neutralization quick and thorough. This speed can mean the difference between a minor issue and a devastating breach. Companies with 24/7 helpdesk support solve problems faster than those using standard business-hours support.
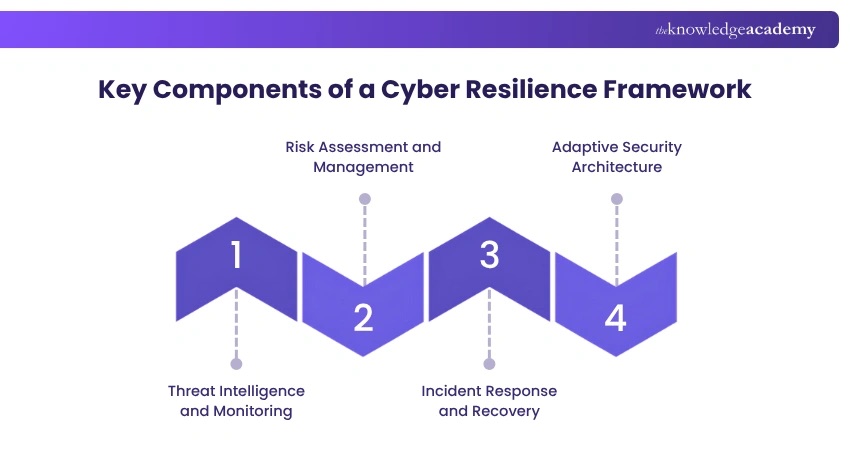
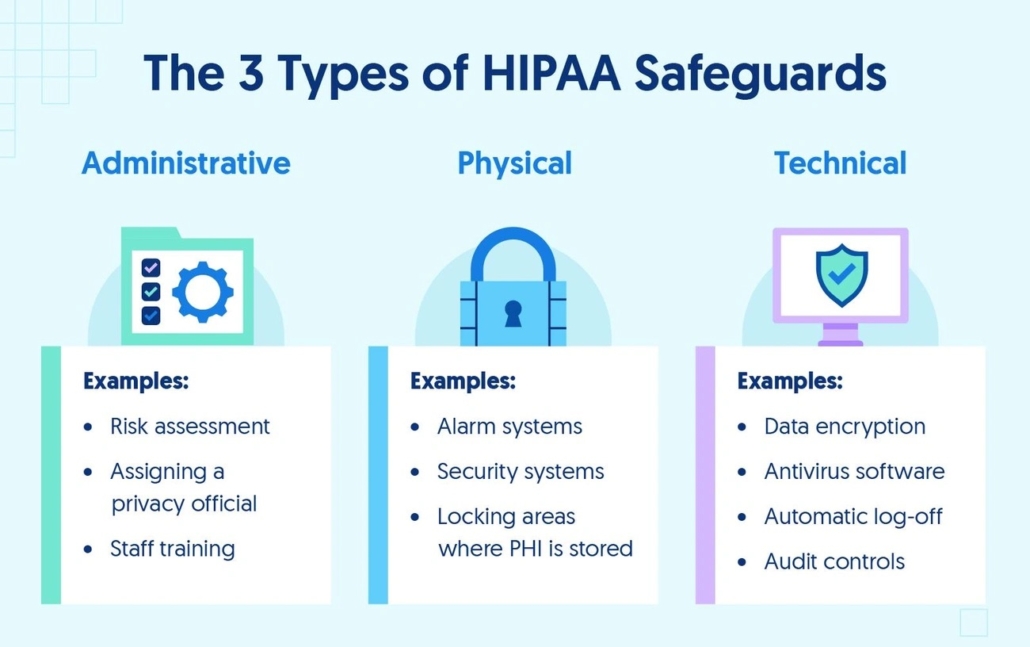
Cybersecurity that meets compliance standards
Great service providers know cybersecurity and compliance work together. They help companies guide through industry-specific regulatory frameworks such as:
- PCI DSS for credit card processing (50+ security controls)
- HIPAA for healthcare information (100+ security controls)
- FISMA for federal information systems (1000+ controls)
Poor compliance makes breach costs worse, with companies paying $2.3 million more for data breaches. Quality managed services create automatic audit trails and log every security event, investigation, and response—crucial records for compliance audits.
Modern cybersecurity needs separate IT infrastructure and security teams. Leading providers offer dedicated security operations centers (SOC) that watch networks using security information and event management (SIEM) systems.
Strategic IT leadership and virtual CIO services
Virtual CIO (vCIO) services mark the progress in IT management and provide executive-level tech guidance without a full-time CIO’s cost. Companies can get technology guidance, budget planning, and multi-year IT roadmaps that match business goals for a fixed monthly fee.
A vCIO turns IT from basic support into a key business strategy component. This reflects the growing need for IT leaders to become strategic partners who can arrange technology initiatives with broader company goals.
Virtual CIOs bring several strategic benefits:
- Strategic roadmaps that create competitive advantages
- Technology use that speeds up business goal achievement
- Digital transformation through streamlined processes
- Cost analysis and IT budgeting for smart investments
This strategic guidance helps companies reduce technical debt by simplifying complex IT programs and limiting unnecessary system changes—key factors for scaling and future-proofing tech environments.
Cloud integration and scalability benefits
Cloud integration connects various data sources to boost enterprise modernization. Information from different environments works as one system. Companies can access their data from any device, anywhere, with unified and cohesive views.
The advantages go beyond continuous connection. Cloud integration removes data silos in traditional systems and enables smooth information sharing across departments. Integrated systems offer one source of truth by combining data from multiple platforms, giving leaders real-time access to useful insights.
Cloud platforms adapt to growing business needs without big hardware investments. Unlike traditional servers needing physical upgrades, cloud platforms use auto-scaling and load balancing to handle large data increases without extra storage.
These capabilities help shift focus from narrow metrics to strategic business results. Next-generation managed services prefer metrics that match strategic business and IT goals instead of traditional IT measurements—turning technology from a cost center into a business value driver.
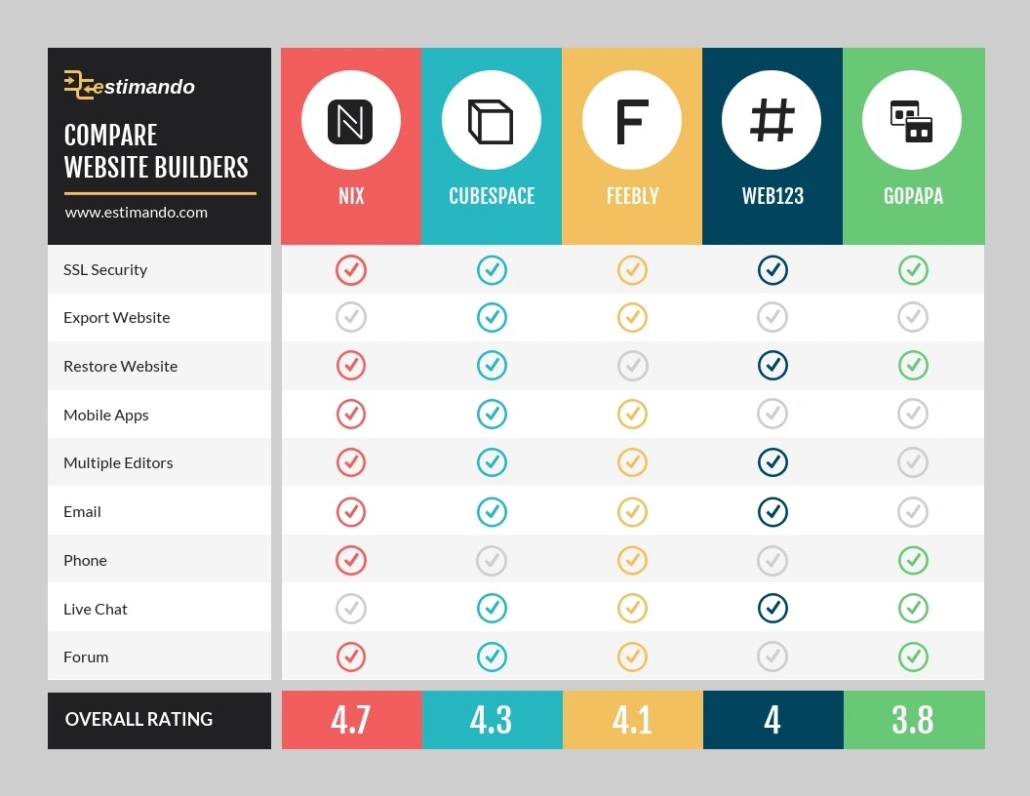
How to Evaluate IT Managed Services Near You
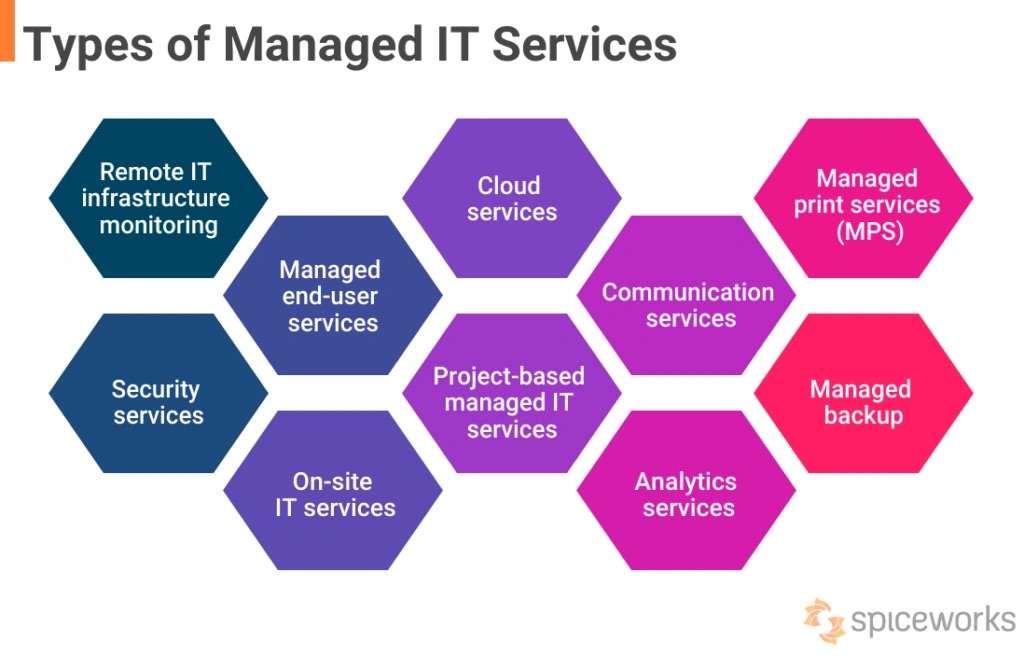
Image Source: Spiceworks
Businesses need a structured approach to pick the right IT managed services provider. Price comparisons alone won’t cut it. Your business technology deserves careful vetting to find a partner that supports your growth and security needs.
5 questions every business should ask
These five key questions will help you identify the right partner for your IT services:
- What are your response and resolution times? The best providers offer 24/7/365 monitoring with clear service level agreements (SLAs) for different issue severities. Ask for specific metrics – top providers can share their average ticket resolution time and first-call resolution rate.
- What security protocols and compliance frameworks do you support? Your provider must understand your industry’s regulatory requirements, whether it’s HIPAA for healthcare, PCI DSS for payment processing, or CMMC for defense contractors. Get specifics about their internal security practices—ask about SOC 2 type 2 audit completion or CMMC standards compliance.
- Do you offer local on-site support? Some issues need physical presence despite remote capabilities. Find out how quickly technicians can reach your location during emergencies. Local office providers typically respond faster on-site than national corporations.
- What is your approach to strategic technology planning? The best partners go beyond break-fix support by offering proactive services and strategic guidance. They should use advanced analytics to prevent incidents by studying failure patterns across platforms.
- Can you provide references from similar businesses? Ask for testimonials and references from clients in your industry. Direct conversations with existing customers reveal ground experiences and the provider’s approach to challenges.
Checklist for compliance and security readiness
This complete checklist helps verify your potential IT partner’s security and compliance capabilities:
Security Measures Assessment:
- Formal, documented cybersecurity plan
- Physical and network security protocols
- Penetration testing capabilities
- Automated patch management procedures
- Advanced threat detection using AI and machine learning
- Security awareness training for employees
Compliance Verification:
- Experience with relevant regulations (GDPR, HIPAA, PCI DSS)
- Documented internal security policies
- Disaster recovery plan with tested procedures
- Data privacy protections that match evolving regulations
- Mean Time to Recovery (MTTR) metrics for outage scenarios
Service Level Expectations:
- Clear SLAs with uptime guarantees
- Transparent termination clauses
- Insurance coverage details
- Flexible pricing models
Sensitive sectors like healthcare and financial services need extra security attention. Your provider should use resilient encryption, data protection measures, and comply with standards like GDPR or HIPAA.
How to assess industry-specific experience
A provider’s industry expertise shapes service quality. Here are key factors to assess:
Verify Depth of Experience: The provider’s work with similar businesses in size, scope and industry enables them to spot industry-specific challenges and create tailored solutions [89, 99].
Examine Certifications and Partnerships: Industry-relevant technical certifications and technology vendor partnerships show their commitment to specialized expertise.
Assess Regulatory Knowledge: Each industry faces unique compliance needs. Your provider needs deep knowledge of your business regulations—from HIPAA in healthcare to PCI DSS for payment card handling.
Review Case Studies: Ask for specific examples of how they solved problems for businesses in your industry. Case studies show their problem-solving approach and industry expertise.
Evaluate Vendor Management: Leading providers maintain strong relationships with top technology vendors. This gives them insights into product development and new technologies. Their vendor-neutral position helps them recommend the best solutions rather than pushing specific products.
Get Your Free IT Assessment — See Why Businesses Across Ohio, the MidWest & Texas Rely on CTMS IT.
The right IT managed services provider combines technical skills, industry knowledge, and strategic vision. You need a technology partner whose expertise covers both maintenance and strategic guidance that matches your business goals. These criteria will help you find a provider ready to support your current needs and future growth.
Future-Proofing Your IT Managed Services for 2026 and Beyond
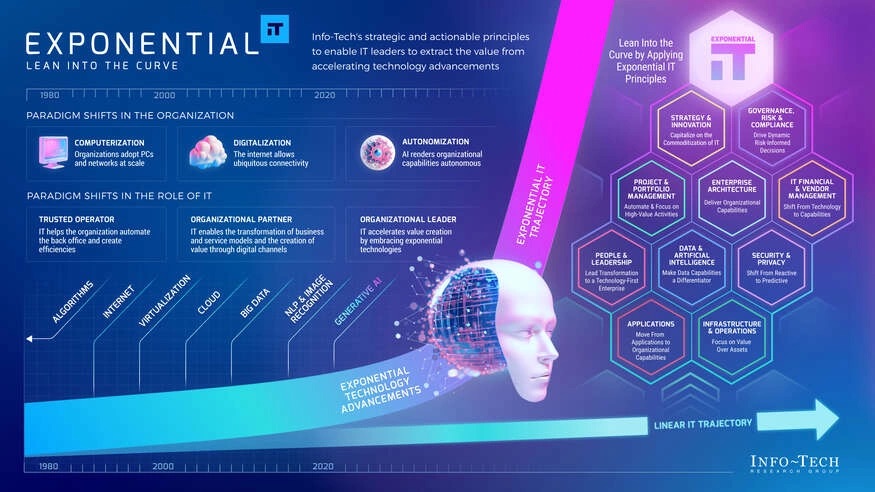
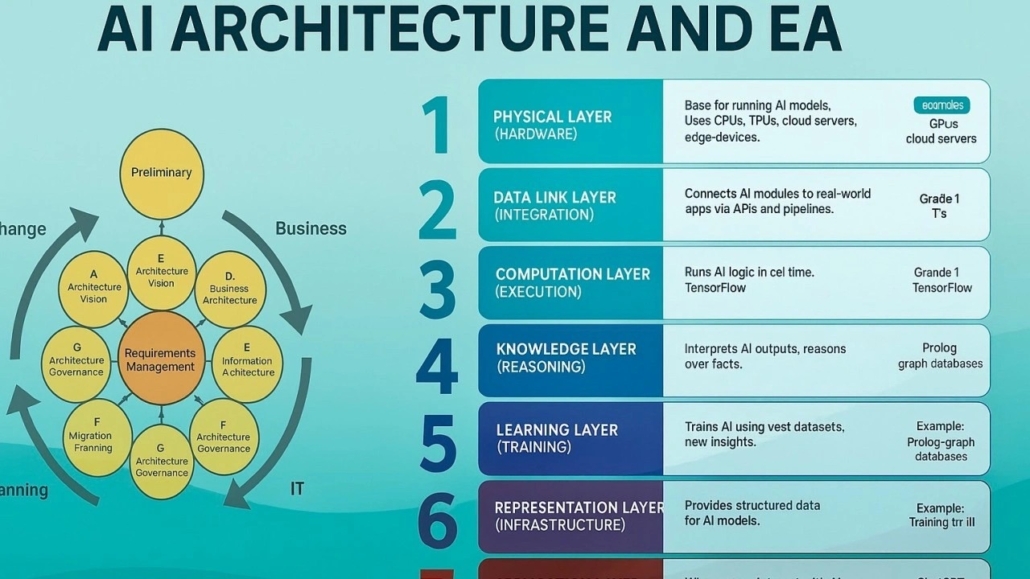
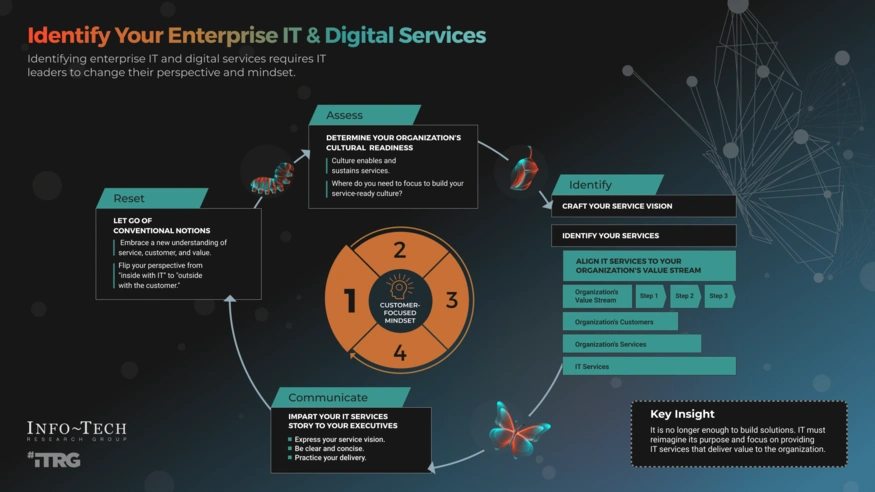
Image Source: Info-Tech
The digital world of IT managed services continues to change faster as we look toward 2026. New technologies are changing how businesses protect and optimize their digital infrastructure. Smart organizations need to get ready for major changes in service delivery models to stay ahead of competitors.
AI-driven IT management and automation
AI has changed IT support from reactive to predictive. About 95% of enterprises plan to spend more on AI, while 83% are speeding up their automation projects. This investment shows results – organizations using AI report better productivity (98%), profitability (97%), and work quality (94%).
AI has become a core part of managed services. It doesn’t replace human expertise but gives IT teams tools to deliver better results. The main capabilities include:
- Predictive analytics that help find root causes and make troubleshooting precise
- Smart ticket routing and automatic fixes to solve problems faster
- Removal of repetitive manual tasks to reduce errors and speed up changes
Agentic AI will change the game for IT operations in 2026. These systems can complete tasks without human input, and senior executives see this as the most promising generative AI development. The model might change from AI helping humans to humans helping AI, which would transform how IT management works.
Adapting to evolving compliance frameworks
New regulations are becoming more complex along with AI breakthroughs. Compliance will grow beyond simple checklists to detailed governance frameworks by 2026. Data privacy remains the top AI concern for 69% of executives – a sharp rise from 43% in just six months.
Digital provenance will become essential. Companies need to verify the origin, ownership, and integrity of software, data, and media. Those who don’t invest in these capabilities might face billions in sanctions by 2029. Many businesses now use “sovereign AI” to keep data, model weights, and computing resources within specific regions.
Modern service providers help organizations direct through this complexity by offering:
- Automated compliance reports and documentation
- Live monitoring for regulatory compliance
- Expert guidance on GDPR, HIPAA, and new AI regulations
Why proactive IT is the foundation for innovation
The move to proactive IT management marks a fundamental change in managed services. Old reactive methods that fix problems after they happen are giving way to preventative strategies powered by AI and machine learning.
Proactive IT management cuts downtime by finding and fixing system issues early. Businesses can avoid surprise repair costs and emergency fixes while staying protected from new threats. Companies that use proactive monitoring fix technical issues much faster.
Proactive IT will expand through 2026 and beyond by using:
- AI and machine learning to analyze data and identify patterns live
- Predictive maintenance to spot system failures before they happen
- Advanced cybersecurity tools to catch and stop threats early
This proactive approach lets businesses create new solutions instead of just responding to technical problems. One IT leader put it well: “When your IT environment is stable and well-managed, your team will have more time and energy to create”.
Smart businesses that adopt these forward-thinking approaches now will grow and stay competitive in the complex digital world of 2026 and beyond.
Comparison Table
| List Item | Key Focus | Main Benefits | Notable Statistics | Critical Features | Industry Impact |
|---|---|---|---|---|---|
| Why ‘Near Me’ Matters More Than Ever | Local service delivery and proximity | – Quicker response times\n- Better local market insights\n- Tailored service | – Local MSPs: 2-4 hours response\n- National providers: 24-72 hours response | – On-site emergency response\n- Face-to-face communication\n- Local compliance expertise | Unique end-user experience and stronger business ties |
| The Hidden Cost of Poorly Managed IT | Money lost from IT failures | – Stopping revenue loss\n- Avoiding compliance fines\n- Less risk | – $5,600 per minute downtime cost\n- 277 days average breach detection time\n- $4.45M average breach cost | – Emergency IT support\n- System recovery\n- Data restoration | 43% of companies close right after major data loss |
| What World-Class IT Managed Services Actually Deliver | Detailed IT solutions | – Round-the-clock monitoring\n- Compliance management\n- Expert guidance | – 15.6 minutes average response time\n- 50+ security controls for PCI DSS\n- 100+ for HIPAA | – Cloud integration\n- Virtual CIO services\n- Cybersecurity monitoring | Shifts from cost center to business value driver |
| How to Review IT Managed Services Near You | Service provider assessment | – Quality checks\n- Less risk\n- Smart provider choice | Not specifically mentioned | – Response time checks\n- Security protocol review\n- Compliance framework check | Sector-specific know-how and custom solutions |
| Future-Proofing Your IT Managed Services for 2026 and Beyond | Forward-looking IT strategy | – AI-driven management\n- Automated compliance\n- Smart maintenance | – 95% of enterprises increasing AI spending\n- 83% accelerating automation\n- 69% concerned about data privacy | – Predictive analytics\n- Intelligent ticket routing\n- Digital provenance | Less downtime and better innovation potential |
Conclusion
Choosing the right IT managed services provider will be crucial to business success by 2026. Local providers offer clear advantages over national ones. Their proximity brings faster responses, better knowledge of local rules, and personal attention when systems crash. Companies lose $5,600 every minute during outages, while data breaches cost an average of $4.45 million each.
Smart business leaders take time to evaluate IT partners instead of rushing to pick the cheapest option. Top providers offer 24/7 monitoring, strong cybersecurity, and tech guidance that turns IT from an expense into a business asset. Get Your Free IT Assessment — See Why Businesses Across Ohio, the MidWest & Texas Rely on CTMS IT. This step reveals gaps in your tech setup before they turn into costly problems.
Technology changes rapidly. AI-driven management and automated compliance systems have altered the map of digital infrastructure management. Companies now realize that old reactive methods are not enough. Advanced monitoring and predictive maintenance are the foundations that support new ideas and growth.
Your search for “IT managed services near me” means more than finding tech support. You need a strategic partner who knows your business world and responds quickly in emergencies. They should help you direct complex compliance requirements. A good local IT partner builds tech systems that strengthen your company. They keep you secure, compliant, and ahead of rivals through 2026 and beyond.
Key Takeaways
Smart businesses are discovering that local IT managed services provide critical advantages over national providers, especially as technology challenges become more complex and costly in 2026.
• Local response beats national scale: Local IT providers deliver 2-4 hour emergency response versus 24-72 hours for national companies, preventing minor issues from becoming major disasters.
• Poor IT management costs $5,600 per minute: Unplanned downtime and security breaches create devastating financial impacts, with average breach costs reaching $4.45 million in 2023.
• 24/7 monitoring prevents 280-day breaches: World-class managed services detect threats in minutes instead of months, dramatically reducing the average hacker dwell time through proactive monitoring.
• AI-driven IT management is the future: 95% of enterprises are increasing AI spending to transform reactive support into predictive maintenance and automated compliance management.
• Strategic evaluation prevents costly mistakes: Ask about response times, security protocols, compliance expertise, and industry-specific experience before selecting an IT partner for long-term success.
The shift from reactive to proactive IT management isn’t just about preventing problems—it’s about creating a technology foundation that enables innovation and competitive advantage. By 2026, businesses with strategic local IT partnerships will be better positioned to navigate evolving compliance frameworks while leveraging AI-powered solutions for sustained growth.